Posted by Virus Bulletin on Nov 12, 2014
Despite better defences, the era of bootkits is certainly not behind us.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Bootkits: past, present & future', by Eugene Rodionov (ESET), Aleksandr Matrosov (Intel) and David Harley (ESET).
Bootkits are about as old as malware itself, with many of the first computer viruses targeting the operating system's boot sector. However, the age of modern bootkits started with the proof of concept 'BootRoot', presented at BlackHat 2005.
Since then, not only have many other more advanced proofs of concept been demonstrated by security researchers, we have also seen several of these techniques being used in the wild by malicious actors.
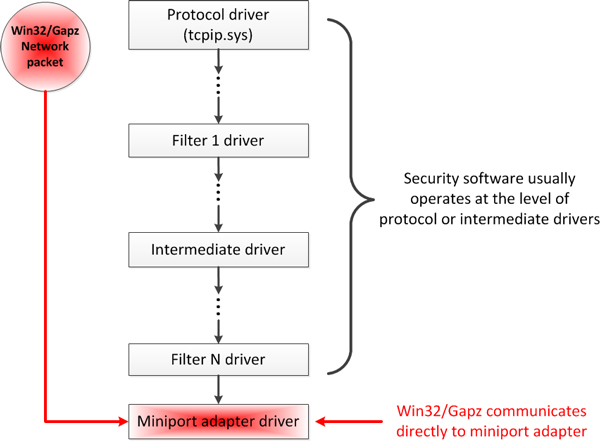
In a paper presented by Eugene Rodionov and Aleksandr Matrosov in Seattle, the authors look at how bootkits have evolved over time. They take a particular look at the techniques used by 'TDL4', 'Rovnix' and 'Gapz', the latter employing one of the stealthiest bootkit infection techniques seen so far.
In the second part of the paper, the focus is on the Unified Extensible Firmware Interface (UEFI), the specification developed to replace BIOS boot software. This poses new challenges for bootkit authors, but as the 'Dreamboot' proof-of-concept bootkit has shown, these challenges are not impossible to overcome.
The authors of the paper then show different attack vectors that UEFI malware can use to take full control of a system.
Finally, they present two tools that those studying possible bootkit infections will probably find useful. CHIPSEC (available at Intel's Github page here) is an open-source framework for analysing the security of PC platforms including hardware, system firmware (including BIOS/UEFI) and the configuration of platform components. To retrieve the content of hidden storage used by many bootkits, the Hidden File System Reader tool (available at ESET's website here) can be very useful.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.