Posted by Virus Bulletin on Jan 8, 2015
Irfan Asrar looks at the security of the operating system used in many IoT devices.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Attack surface analysis of Tizen devices' by Irfan Asrar, a researcher from Intel Security Group.
If you're concerned about the security of the "Internet-of-Things", you should keep an eye on Tizen. The operating system is based on the Linux kernel and is developed by Intel and Samsung under the auspices of the Linux Foundation. It is used on a wide range of devices, from smart TVs to printers, and from smart watches to mobile phones.
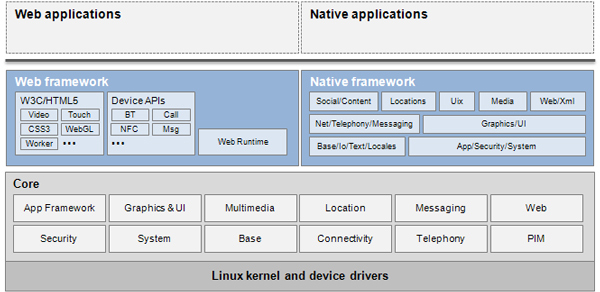
In his VB2014 paper, Irfan Asrar explains how the system is built with security in mind - something that is reflected in how Tizen determines what apps can be installed, and what permissions and access controls these apps have, once installed. It also uses post-install privacy controls, which can be used to deny an already installed app access to user data.
Still, we know all too well that nothing is perfect. Thankfully, Tizen includes a content security framework. This framework, which is developed by McAfee and, like the operating system itself, is open source, can be used by third-party security apps to further harden the security of a device that runs Tizen.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). We have also uploaded the presentation to our YouTube channel.