Posted by Virus Bulletin on Jan 13, 2015
James Wyke looks at malware that takes extra steps to frustrate researchers.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added 'Duping the machine - malware strategies, post sandbox detection' by Sophos researcher James Wyke.
To hinder the automatic detection of malware samples, it is common for malware authors to add mechanisms that detect whether the malware is being run inside a sandbox.
Most malware simply halts execution once it detects that it is running inside a sandbox, but in his VB2014 presentation, James Wyke looked at four malware families (Andromeda, Simda, Vundo and Shylock) that go a step further and employ various kinds of decoy behaviour.
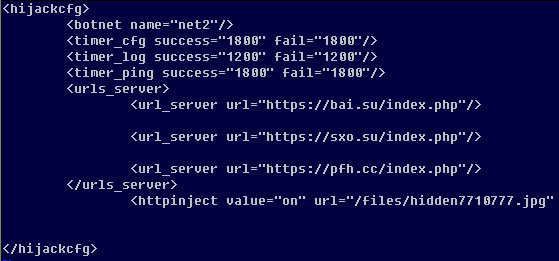
This can vary from performing benign behaviour by connecting to a non-malicious server rather than the real command-and-control server, to returning fake configuration data when such a server receives a request from a sandboxed sample.
In all cases it will hamper detection and frustrate researchers. It could also help the malware authors to build a blacklist of researchers' IP addresses so that, should they harden their environment, they still won't see the real behaviour of the malware.
You can read the paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.