Posted by Virus Bulletin on Mar 2, 2015
Dénes Óvári explains how to store code in lossily compressed JPEG data.
Malformed PDFs have become a common way to deliver malware. Naturally, when this started to happen, anti-virus products began scanning inside PDF files for traces of malicious code and, equally naturally, malware authors started to obfuscate that code to circumvent scanners.
Not everything can be used to store code though. Data streams compressed using lossy compressors like JPXDecode and DCTDecode are deemed unsuitable for storing any kind of code. After all, the lossy compression means one should not be able to retrieve an exact copy of the uncompressed data. For performance reasons, scanners therefore usually ignore this data.
But are they right to do so? Today, we publish a paper by CSIS researcher Dénes Óvári, who found a way to store code as a JPEG image using the DCTDecode filter. His trick, which he explains in the paper, was to encode the data as a greyscale JPEG image, so that no rounding occurs when the images is converted from the RGB to the YCbCr colour space.
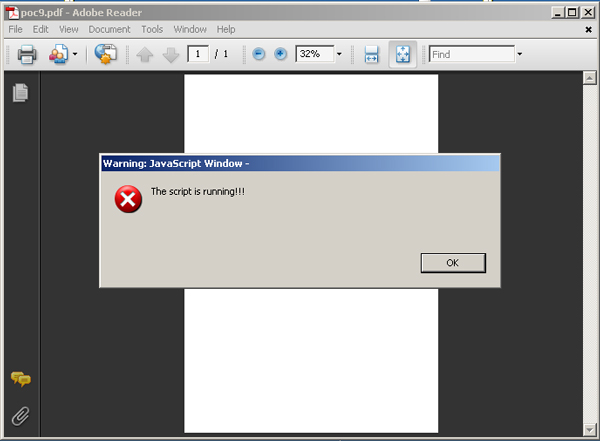
To show that this is not merely a theoretical possibility, Dénes wrote a proof-of-concept where a simple (and in this case harmless) piece of JavaScript code was thus embedded inside a PDF.
You can read the paper here in HTML format or here as a PDF. Remember that all content published by Virus Bulletin can be read free of charge, with no registration required.
Both Adobe and anti-virus vendors were given advance notification of the publication of this paper.
Posted on 2 March 2015 by Martijn Grooten