Posted by Virus Bulletin on Mar 30, 2015
Ruchna Nigam provides an overview of more than 60 mobile malware families.
The rise of mobile malware is still a relatively recent thing, with the first actual mobile botnets not appearing until the beginning of this decade.
However, since then things have changed quickly, and today there are more than one million known mobile malware samples (though not families) in existence and mobile malware is almost as common as malware targeting desktops (even if there are some fundamental differences between the two).
Today, we publish a paper by Fortinet researcher Ruchna Nigam, in which she presents a timeline of mobile botnets.
Not only does Ruchna list more than 60 mobile botnets (including well-known names such as Zitmo, NotCompatible, Xsser and DroidKungFu) and provide basic information on all of them, she also takes a closer look at some particularly interesting variants.
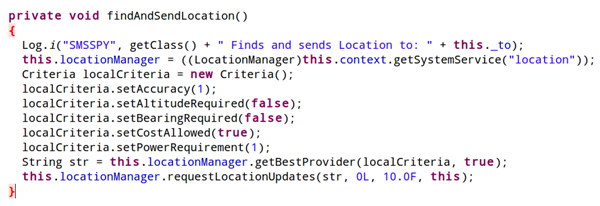
Moreover, in her paper Ruchna takes a look at how mobile malware, not unlike malware targeting desktop operating systems, uses anti-debugging tricks, code obfuscation and traffic encryption.
She finishes her paper by providing some statistics on mobile botnets, including the C&C channel used, the motivation behind the malware and the kinds of certificates used to sign the APK files.
You can read the paper here in HTML format or here as a PDF. (Remember that all content published by Virus Bulletin can be read free of charge, with no registration required.)
Ruchna's paper was originally presented at and published by Botconf 2014 and was republished with permission. My review of the 2014 edition of Botconf can be found here. The call for papers for its third edition, which will take place 2-4 December in Paris, France, can be found here.
