Posted by Virus Bulletin on Jun 24, 2015
Tool to extract identifiers incorporated into VirusTotal.
The large number of new malware samples found each day hasn't made malware analysis an easier task, and researchers could use anything that helps them automate this task.
Today, we publish a paper by Cylance researcher Brian Wallace, who looks at two globally unique identifiers (GUIDs) found in malware created using .NET, which can help link multiple files to the same Visual Studio project. He released a Python tool to safely extract these identifiers; the tool has since been incorporated into VirusTotal.
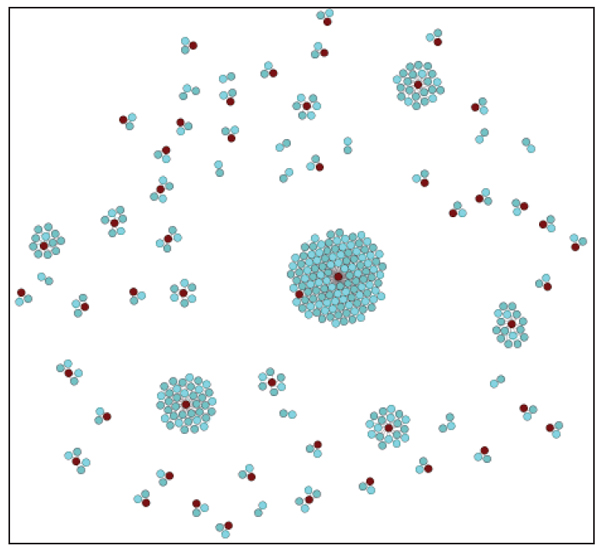
The idea for using these two GUIDs — MVID, which is unique to each build, and TypeLib ID, which is unique to each Visual Studio Project — came during research that was part of 'Operation Cleaver' late last year, where it greatly reduced the number of samples that needed to be reverse-engineered.
Although the GUIDs can easily be extracted from executables, not all methods of doing so are safe; hence Brian has written a tool that does so securely and works cross-platform. The tool, GetNETGUIDs, has been published on Cylance's GitHub page.
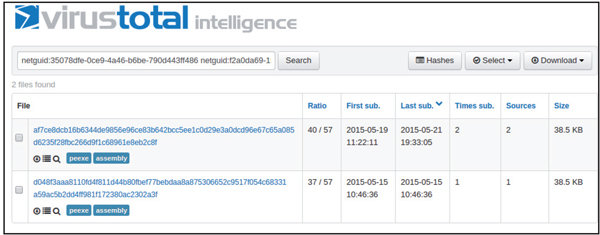
The tool has since been incorporated into VirusTotal, where it can be used to search for files with the same MVID and/or TypeLib ID.
You can read the paper here in HTML format or here as a PDF. Remember that all content published by Virus Bulletin can be read free of charge, with no registration required.