Posted by Virus Bulletin on Jul 8, 2015
Lists of customers, source code and zero-day vulnerabilities made public.
The biggest security story of this week, and probably one of the biggest of the year, is the hack of Italian company Hacking Team. The story has been covered widely, for instance by Wired, Ars Technica, The Register and Forbes, as well as by many mainstream media outlets.
Security professionals rarely publicly condone hacks of companies, but in this case many have been happy to make an exception. Not only can Hacking Team's products (which perform unauthorised actions on a target's computer or device) unambiguously be described as malware, the company also has a reputation for turning a blind eye when selling these products to governments with a dubious reputation when it comes to respecting human rights.
Indeed, the leaks confirm that Hacking Team sold their spyware to countries such as Sudan, Ethiopia and Bahrain. The leaks also made the source code of the companies' products public and revealed passwords that weren't exactly up to scratch. On top of that, a number of zero-day vulnerabilities used by the company have been found, including one in Adobe's Flash Player, which researcher Kafeine reports has since been added to no fewer than three different exploit kits. Adobe has released an advisory and promises to release a patch later on Wednesday.
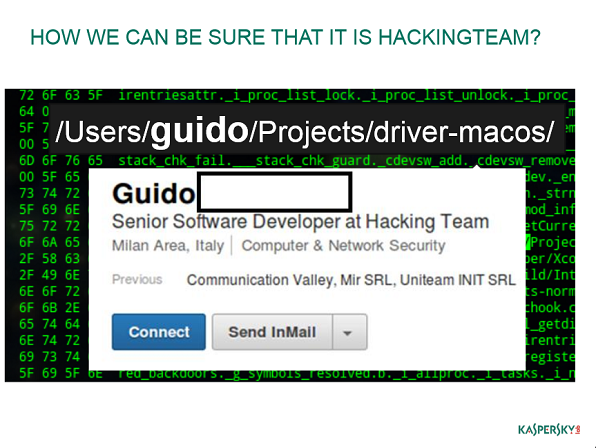
Hacking Team is well known among security researchers. At VB2013, Kaspersky researcher Sergey Golovanov presented a paper on Hacking Team and UK-based Gamma International. The video of that presentation is worth watching, not least for the song Sergey had written in 'honour' of the malware authors at those companies.
In 2014, Hacking Team was the topic of a three-part research project (1, 2, 3) by researchers from Citizen Lab. Their investigations had already uncovered many of the facts that have now become public and that had hitherto been denied by Hacking Team. The research was nominated for last year's Péter Ször Award.
At VB2015, one of the authors of the research, Claudio Guarnieri, will give a Small Talk 'Helping the Helpless: Targeted Threats to Civil Society', in which he looks at what can be done to help those whose governments are using tools like Hacking Team's to spy on them — something which in many countries can have grave consequences.