Posted by Virus Bulletin on Jan 19, 2016
Microsoft, Dell SecureWorks researchers analyse malware targeting Active Directory servers.
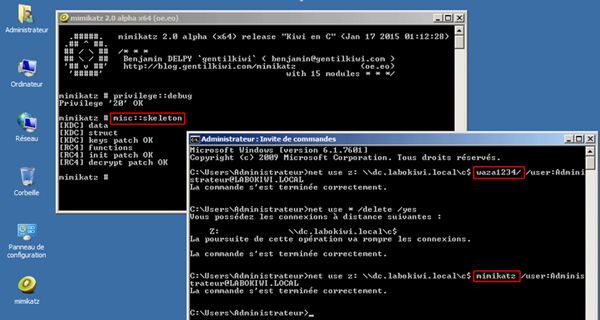
A year ago, researchers from Dell SecureWorks discovered a new kind of malware, dubbed 'Skeleton Key', that was used in targeted attacks.
The malware, which was installed on the target's domain controller, allowed the attacker to login as any user and thus perform any number of actions.
At VB2015, Microsoft researchers Chun Feng, Tal Be'ery and Michael Cherny, and Dell SecureWorks' Stewart McIntyre presented the paper "Digital 'Bian Lian' (face changing): the skeleton key malware". Today, we publish their paper as well as the video of their presentation.
You can read the paper here in HTML-format, or download it here as a PDF, and find the video on our YouTube channel, or embedded below.
Are you interested in presenting your research at the upcoming Virus Bulletin conference (VB2016), in Denver 5-7 October 2016? The call for papers is now open.