Posted by Martijn Grooten on Mar 2, 2016
While SMS has been declared dead many times, the service remains frequently used - and abused.
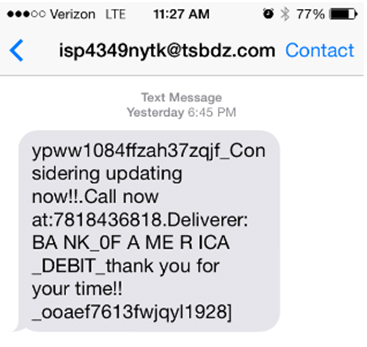
In a paper presented at VB2015 in Prague, Adaptive Mobile researcher Cathal Mc Daid looked at fraudulent SMS campaigns, in particular those targeting banking users in North America.
He showed how these campaigns tend to target specific banks and specific regions, especially those on the East Coast, and also looked at how, similar to what we have long seen in email spam, the messages keep changing in subtle ways, to stay one step ahead of detection.
You can read his paper "Mobile Banking Fraud via SMS in North America: Who's Doing it and How" here in HTML format or here as a PDF, and find the video on our YouTube channel, or embedded below.
Are you interested in presenting your research at the upcoming Virus Bulletin conference (VB2016), in Denver 5-7 October 2016? The call for papers is now open.