Posted by Martijn Grooten on Oct 18, 2016
VB2016 took place almost two weeks ago, since when we have had many requests to publish the papers presented at the conference, as well as the videos of those presentations. Virus Bulletin is all about bringing security experts together and making relevant information accessible to them and for that reason, subject to authors' permission, we plan to publish the papers and videos from VB2016 during the coming months.
We start today with a paper that was not presented at VB2016. 'The TAO of Automated Iframe Injectors - Building Drive-by Platforms For Fun' was written by Blue Coat researcher Aditya K. Sood and was listed as a reserve paper, but circumstances prevented the author from making the trip to Denver to present it.
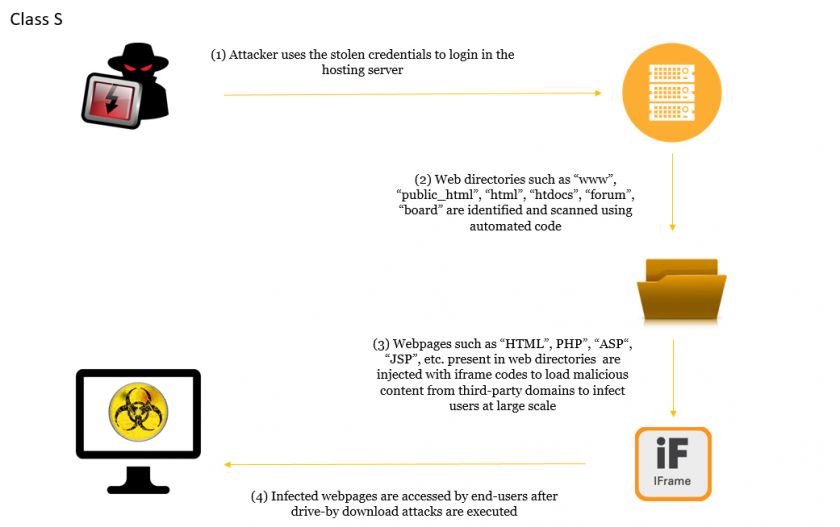
In the paper, Aditya looks at 'iframe injectors', which are responsible for the delivery of many active drive-by downloads and have long been a plague on the web. The paper looks at how cybercriminals use these tools, discusses their classification and looks at some common variants.
You can read the paper here in HTML format, or download it as a PDF here.