Posted by Martijn Grooten on Sep 9, 2016
If you are wondering whether you really live in the future: we need to be concerned about the security of Internet-connected power outlets.
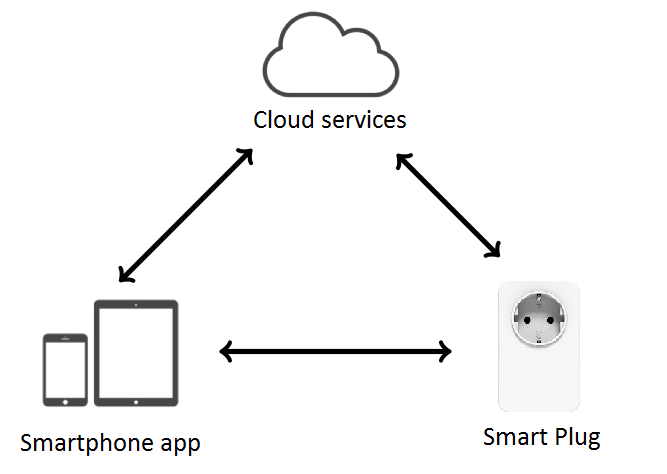
Such devices are the subject of a VB2016 paper by four researchers from Bitdefender in Romania: George Cabău, Radu Basaraba, Dragoș Gavriluț and Ciprian Oprișa. While the devices may not appear to offer a lot of possibilities for those with malicious intentions, the fact that they can turn any device whose power is controlled by them into a "smart device" means that their security should concern us.
Unfortunately, security didn't appear to have been a concern for the developers of these devices as, when looking at four "smart" outlets, the researchers found issues with all of them, including two that could be hacked remotely. Worse, when the manufacturers were contacted, they didn't show much interest in fixing the issues, or answering the researchers' calls.
The researchers will discuss these issues, some of which are embarrassingly simple, on Friday 7 October at VB2016.
VB2016 starts in four weeks' time and registration is still open. For more on IoT security, there is the presentation Mobile Applications: a Backdoor into Internet of Things? by Fortinet researcher Axelle Apvrille, which we previewed last week.