Posted by Martijn Grooten on Apr 25, 2017
We all know the risks of having a device infected with malware: an anonymous adversary far away can encrypt your files and hold them to ransom; they can steal your personal data and sell it online; or they can steal your money directly from your online financial services.
But imagine if the adversary is neither anonymous nor far away, but an abusive (ex-)partner. They may not be after your money or your identity, but they will be able to see what you are doing, who you are talking to, and where you are going.
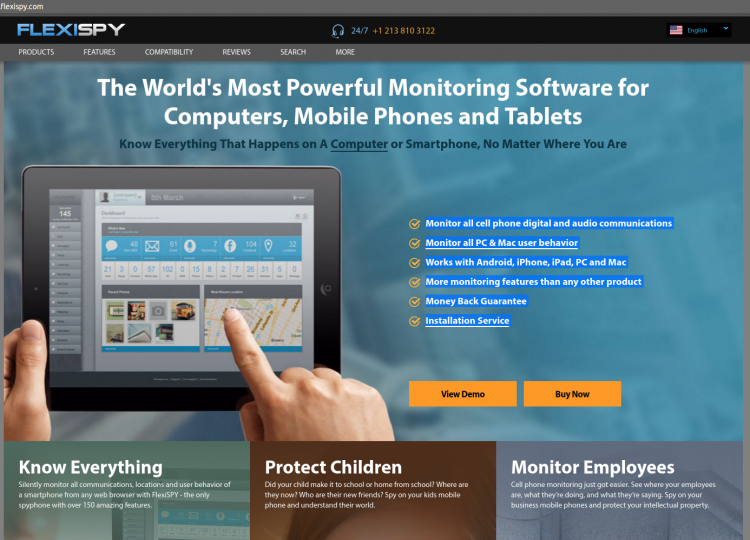
If that sounds creepy, that's because it is. Unfortunately, it is a very real threat for very many people: as VICE Motherboard shows in an investigative series on consumer spyware (also known as 'stalkerware' or 'spouseware'), such software is widely available, relatively cheap, and worryingly popular.
Though many of the software's customers will have no intent on harming their target, there are cases where such malware has been linked to serious cases of domestic violence. This alone should be enough to make anyone care about this issue.
But if you are working in security, there is another reason why you should care: the threat model is very different from the one we usually consider. How well does your authentication mechanism work against an adversary who has physical access to the device and to the 2FA token, and who may know the answers to all the victim's security questions? How does your security software, which may well detect the spyware as malicious, fare against an adversary who disables it when installing the spyware?
I would recommend to anyone that they read the series at VICE Motherboard, which gives an excellent insight into how the makers of spyware operate. I would also recommend you come to VB2017, where Joseph Cox, one of the series' authors, will give a presentation on this very subject.
Register for VB2017 now to see Joseph and dozens of other security experts from around the world present on all aspects of the security threat landscape. Register before 30 June to get a 10% Early Bird discount.