Posted by Martijn Grooten on Apr 24, 2017
Anyone who has ever analysed malware through its network communications will knows that this often involves ad-hoc scripts in languages like Python or Perl to decode the traffic. After all, for somewhat understandable reasons, there is no standard C&C protocol for malware.
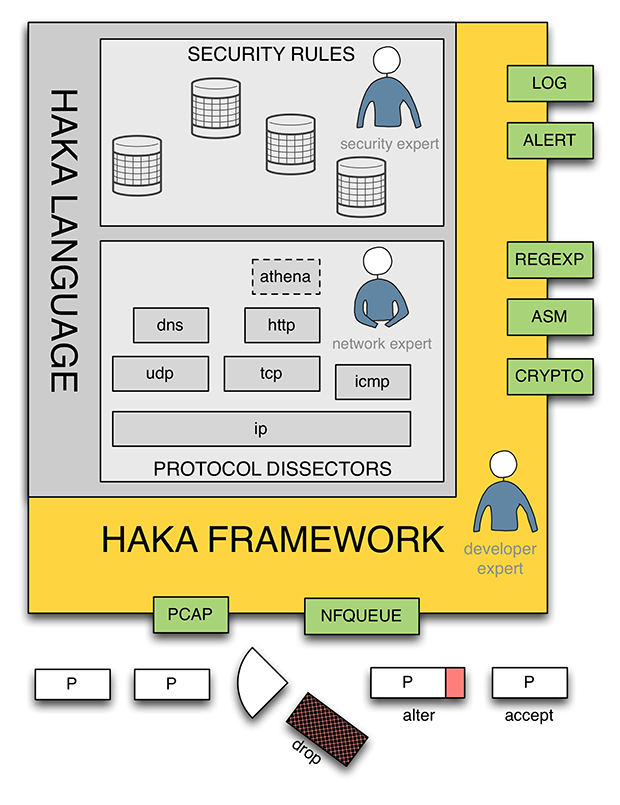
If you regularly find yourself in this situation, you may want to have a look at Haka, an open-source language for monitoring, debugging and controlling malicious network traffic. At VB2016 in Denver, Stormshield researchers Benoît Ancel and Mehdi Talbi, who wrote Haka, presented the paper 'Debugging and Monitoring Malware Network Activities with Haka', in which they introduced Haka and explained how it can be used.
We have now published the paper in both HTML and PDF format. We have also uploaded the video recording of their presentation to our YouTube channel.
For 26 years, the Virus Bulletin Conference has been the place where security researchers share their tools, tricks and ideas to further the fight against online malicious activity. VB2017, which will take place in Madrid, 4-6 October this year, will be no exception – check out the programme and make sure you grab your ticket before 30 June for the early bird discount!