Posted by Martijn Grooten on Jul 27, 2017
This week, the NoMoreRansom project celebrates its first anniversary and can look back to subtle but important successes in the fight against ransomware.
![]()
The advice from security experts to ransomware victims tends to be twofold: keep backups, and don't pay the ransom. The former is indeed very important advice, but isn't really helpful when ransomware has already encrypted all one's important files and the task of making a backup never left the 'to-do' list. The latter is also very sensible advice, as one wouldn't want to pay possibly unreliable criminals – except as a last resort.
Victims tend to be very bad at knowing what constitutes the last resort. Maybe decryption isn't possible because the authors have completely messed up, or had other motives for encrypting the victim's files (on his blog, Bart Parys, a VB2017 speaker, provides a good overview of such motives). Maybe files aren't encrypted at all and the ransomware merely claims they have been.
Or maybe mistakes made by the malware authors, a change of heart among those authors, or the discovery of private keys by law enforcement has led to the release of a recovery tool. It is here that NoMoreRansom's website is particularly useful: victims can upload encrypted files, the site attempts to identify the ransomware with which they have been infected, and determines whether it is one of dozens for which a decryption tool is available.
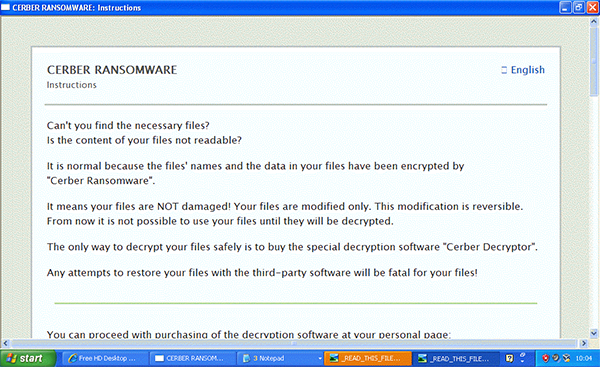
Unfortunately, decryption tools aren't available for all ransomware variants and some of the most common, such as Locky (the subject of a VB2016 paper) and Cerber (the subject of a VB2017 paper) appear to avoid making mistakes. A site like NoMoreRansom can't change this, and ultimately it is up to the victim of such ransomware to decide whether to take the risk of paying. But the project does at least reduce the chances of someone paying for nothing.
When I first joined the world of IT security a decade ago, I was genuinely surprised to see competitors working together to fight a common threat. The NoMoreRansom project, which includes more than 100 partners from the private and public sector, is an excellent example of such cooperation and it will have made a real different for many ransomware victims.