Posted by Martijn Grooten on Nov 21, 2017
While a domain name is really just a short string, this string comes with a large amount of implicit metadata: the registration date; the IP address(es) the domain currently points to and has pointed to in the past; the associated name servers; past activity observed using the domain.
For this reason, domain names play an important role in the fight against malware and other kinds of malicious activity, whether in blacklists of domains used in spam emails or security products that consider the domain in order to determine whether a particular website is malicious.
This is an important reason why compromised websites play a significant role in many web-based malware campaigns. As security blogger Troy Hunt pointed out in a recent blog post, "Nobody ever suspects daffodils."
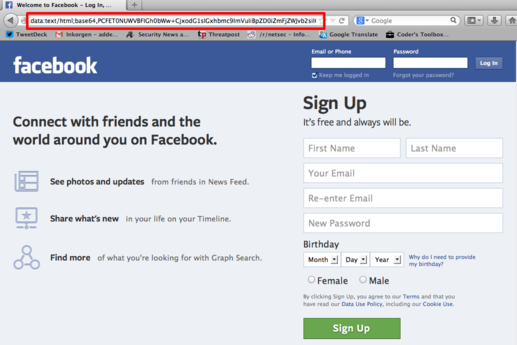
But there is another trick used in some malicious web activity that manages to avoid domains altogether: data URIs.
These URIs start with data: and contain the full content of the web object (e.g. an image or an HTML page), usually Base64-encoded. For example, a very simple HTML page could look like this:
data:text/html;base64,PGh0bWw+CjxoZWFkPjx0aXRsZT5IZWxsbyB3b3JsZDwvdGl0bGU+PC9oZWFkPgo8Ym9keT4KSGVsbG8sIDxiPndvcmxkPC9iPiEKPC9ib2R5Pgo8L2h0bWw+Cg==
There are many legitimate uses for data URIs, but they are increasingly being used for malicious purposes, in particular phishing attacks, where they serve the phishers with a means of embedding the full website in their email without having to depend on created or compromised (and in both cases blacklist-able) web servers.
Earlier this year, a Gmail phishing campaign made use of this technique, while a few years ago, security researcher Andreas Lindh used the same trick to demonstrate a vulnerability in various 3G/4G USB modems.
This malicious use of browsers has not gone unnoticed by browser developers: Firefox developer Mozilla announced that, as of version 59 of the browser, it will stop rendering data URIs in certain scenarios, such as those where a data URI containing HTML is opened in the browser, or when a data URI containing JavaScript is loaded by a website. Here, Firefox follows other browsers, such as Chrome and Edge, which have already made similar changes.
There are, no doubt, legitimate cases of data URI usage that will be frustrated by browsers becoming less tolerant of them. But on balance this seems a good move: it will force phishers and other cybercriminals to use domain names which, from their point of view, are the weak link in many a campaign.