Posted by Martijn Grooten on Nov 22, 2017
Malicious Internet traffic, such as botnet C&C traffic, is easily recognized if it uses known bad domain names, or known bad IP addresses. This is why botnets constantly change the domain names, and often also the IP addresses they use, thus trying to stay one step ahead of the defenders.
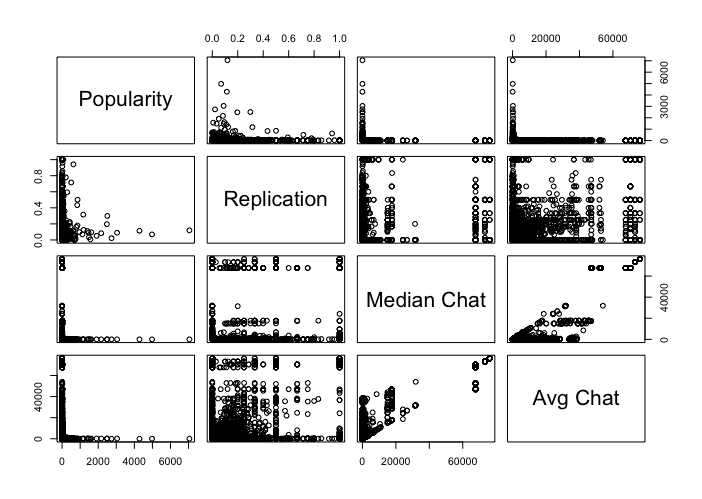
Enter big data: infected devices to tend to show behaviour that makes them stand out from the crowd. For instance, such machines tend to be very 'chatty' (i.e. make a lot of connections) with domains that are otherwise not particularly 'popular'.
This terminology comes from a VB2017 paper by Cisco Umbrella (formerly OpenDNS) researchers Dhia Mahjoub and David Rodriguez, who presented a new approach to detecting infected machines as well as botnet networks in the very large haystack of the Internet.
Today, we publish their paper 'Beyond lexical and PDNS: using signals on graphs to uncover online threats at scale' in both HTML and PDF format; we have also uploaded the video of their paper to our YouTube channel. If you're into big data and not afraid of some serious mathematics, make sure you read the paper and watch the video.