Posted by Martijn Grooten on Jun 11, 2018
A little over a year ago, one of the defining security events of the decade occurred: the WannaCry outbreak. A damaging and destructive cyber attack that hit the UK's National Health Service particularly hard.
The high infection rate of WannaCry was in large part thanks to its implementation of 'EternalBlue', an exploit of a remote code execution vulnerability in Windows SMB. What made the story rather juicy is that EternalBlue had initially been written by the NSA and had been made public a month prior to the WannaCry outbreak, as part of one of the Shadow Brokers' dumps. This particular dump included a number of other exploits and tools, one of which was the 'DoublePulsar' backdoor.
Though a kill switch prevented WannaCry from doing any further damage, both EternalBlue and DoublePulsar continue to be used in other malware, with EternalBlue detections going up rather than down.
Given the relevance of these exploits, we are excited to publish a research paper by Pradeep Kulkarni, Sameer Patil, Prashant Kadam and Aniruddha Dolas, researchers from Quick Heal Security Labs in India. In the paper, they provide technical details of EternalBlue, DoublePulsar and other tools from the same toolset. You can find the paper in both HTML and PDF format.
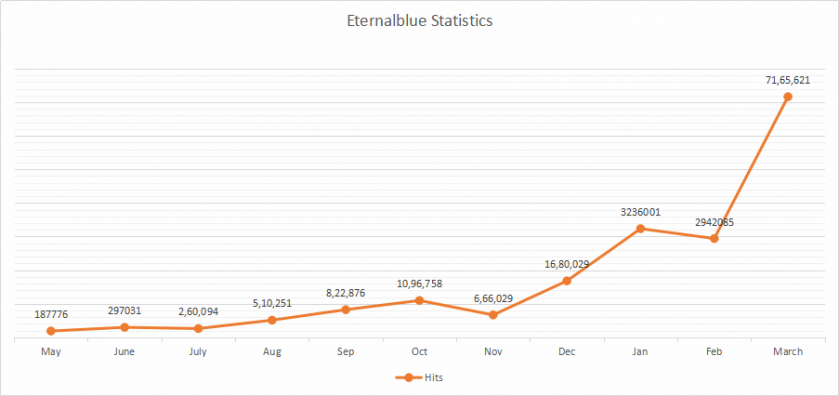 EternalBlue detection statistics.
EternalBlue detection statistics.