Posted by Martijn Grooten on Sep 27, 2018
Today we publish a short article by Ronen Slavin and Michael Maltsev, researchers at Reason Software, one of the partners of VB2018.
In the article, Ronen and Michael dive into the video capturing internals on Windows, and explain how this can be used by a malicious actor to steal images recorded by a computer's webcam.
They then explain how one could build a kernel driver that protects such images, but still allows their use by trusted programs such as Skype.
You can read the article by Ronen and Michael in both HTML and PDF format.
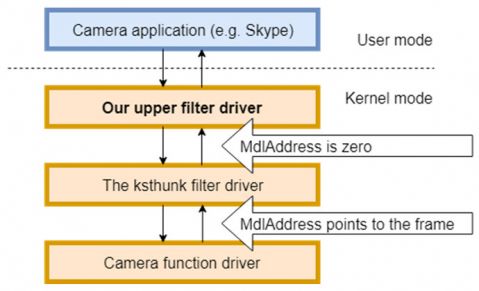
After driver installation.
Those interested in the subject of secretly recording webcam streams should also watch the VB2016 presentation in which Patrick Wardle looked at this subject on Macs.