Posted by Martijn Grooten on Sep 19, 2018
Yesterday, a new report by Citizen Lab looked at NSO Group's Pegasus spyware and its global use. The report is worth a read, for the political implications of the findings, for the interesting methodology used, as well as for the section on the ethics of DNS cache probing.
I have long been a fan of Citizen Lab's publications on digital threats against civil society and I am thus very excited that the Lab's Masashi Crete-Nishihata and John Scott Railton will be speaking on this very topic at VB2018 next month.
Threats against civil society in general, and the use of commercial spyware by governments for this purpose in particular, have long been a favourite topic of VB conference attendees, and there are two more talks on this year's programme that will also cover this particular threat.
Right before the Citizen Lab presentation, ESET's Filip Kafka will present a paper on the resurfaced Hacking Team spyware, and what has changed since the company behind it faced a number of prominent hacks. Filip's research builds on previous work by the aforementioned Citizen Lab on Hacking Team and also complements his VB2017 presentation on FinFisher, another kind of EU-made government spyware with a rather dubious reputation.
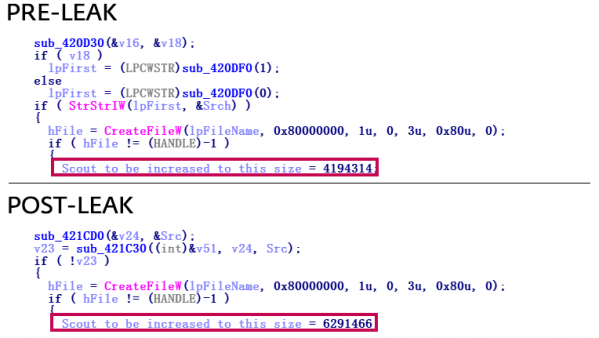
One of many changes made by Hacking Team's malware after the company was breached.
Then on Thursday, CSIS researchers Benoît Ancel and Aleksejs Kuprins will detail their investigation into an actor that appears to have been selling commercial spyware as government espionage spyware and that appears to have cared more about its appearance towards potential customers than about its operational security.
VB2018 takes place in Montreal, 3-5 October. Places are still available, so to make sure you don't miss these important talks, as well as more than 50 others by security experts from around the globe, book your ticket now!