Posted by Martijn Grooten on Sep 21, 2018
In recent years, car hacking has evolved from a mostly theoretical research field involving giggling researchers and scared journalists, to one that actually concerns car owners and manufacturers. It is fitting, then, that at VB2018 next month, two papers will be presented on the subject of car hacking.
Inbar Raz, Security Architect at Argus Cyber Security and a regular VB speaker, will present an overview of the subject, in which he takes away the hype and looks at the actual problem with the (in)security of cars, what has happened in this field so far, and what is likely to happen in the future. The paper and Inbar's presentation are likely to help those who are new to the field understand what really matters.
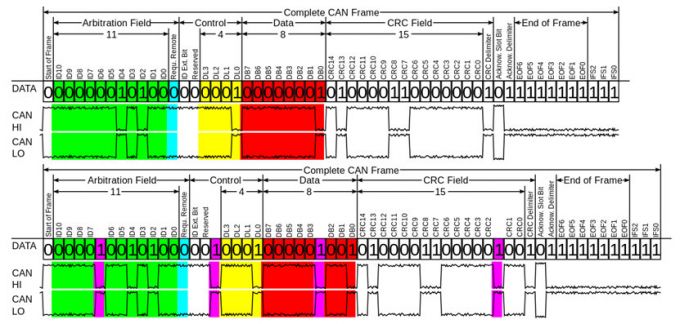 Overview of the CAN bus, the most widely used network connecting various vehicle subsystems.
Overview of the CAN bus, the most widely used network connecting various vehicle subsystems.
One thing that certainly matters is the ability to break into a parked car by exploiting vulnerabilities that exist in the way a car can be controlled remotely. This is one of the examples described in a paper and presentation by Trend Micro researcher Spencer Hsieh, who will look at security issues of Internet of Vehicle (IoV) devices.
To make sure you get to see the presentations by Inbar and Spencer, as well as presentations by more than 50 other security experts on active threats, useful tools and important issues in the world of security, register for VB2018 now!
VB2018 takes place in Montreal, 3-5 October.