Posted by Martijn Grooten on Sep 17, 2018
For a long time IoT-botnets were just one of those things security professionals warned about. Then, with the appearance of Mirai in 2016, they became a reality.
Mirai's success in performing DDoS attacks, combined with the leak of the botnet's source code, has led to a great many descendants, some of which stay closer to the original than others.
At VB2018, Ya Liu and Hui Wang, researchers from Qihoo 360 Technology in China, will present a paper in which they look at how to extract various data from Mirai samples and how this can then be used to classify and track variants of the botnet.
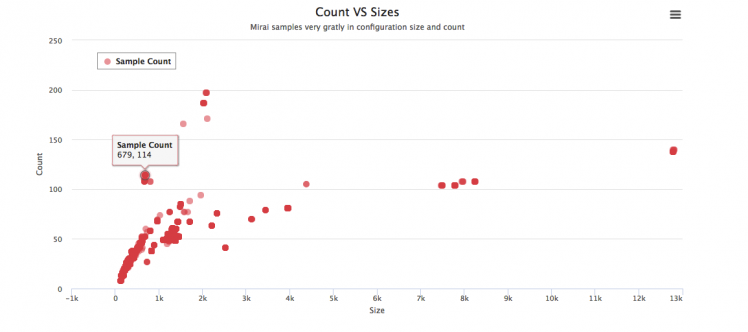 Clustering samples based on configuration count and size.
Clustering samples based on configuration count and size.
But Mirai descendants aren't the only IoT-botnets around. Earlier this year, researchers from Bitdefender in Romania discovered Hide'n'Seek, an IoT botnet noteworthy for its peer-to-peer architecture. The lack of a central command-and-control server makes such botnets harder to take over or shut down.
At VB2018, Bitdefender researchers Adrian Şendroiu and Vladimir Diaconescu will present a paper in which they perform a technical analysis of the botnet, including updates since its first discovery in January, such as added persistence.
VB2018 takes place in Montreal, 3-5 October. Places are still available, so to make sure you don't miss these important talks, as well as more than 50 others by security experts from around the globe, book your ticket now!