Posted by on Oct 17, 2018
With this year's very successful Virus Bulletin Conference (VB2018) now behind us, we plan to continue the tradition of publishing most of the papers and videos of the presentations. We start with 'The Dark Side of WebAssembly', a paper by Symantec researchers Aishwarya Lonkar and Siddhesh Chandrayan that was part of the conference proceedings but, due to circumstances beyond the authors' control, was not able to be presented in Montreal.
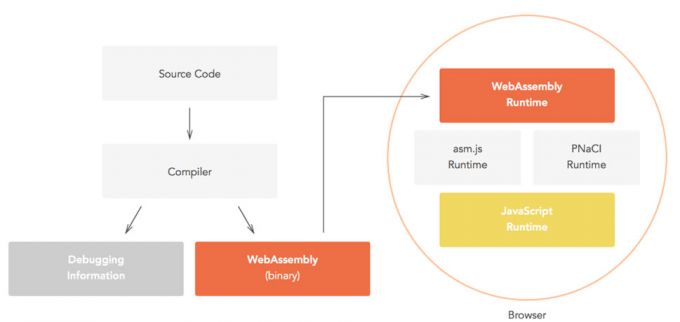
WebAssembly is a relatively recent addition to a web developer's arsenal, giving them the ability to run code nearly as fast as native machine code, thus achieving essential gains in performance. However, malware authors may also have a lot to gain from WebAssembly; it is this that Aishwarya and Siddhesh focus on in their paper.
You can read the paper in both HTML and PDF format.
More on potential issues with WebAssembly can be found in a recent blog post by Natalie Silvanovich of Google's Project Zero and a video by Sophos's Christophe Alladoum, while Forcepoint's John Bergbom explains how to analyse WebAssembly binaries.