Posted by Martijn Grooten on Oct 26, 2018
When it comes to web-based threats, Malwarebytes researcher Jérôme Segura is one of the people to follow. His quarterly reviews of the exploit kit landscape are an essential read for anyone who follows this type of threat.
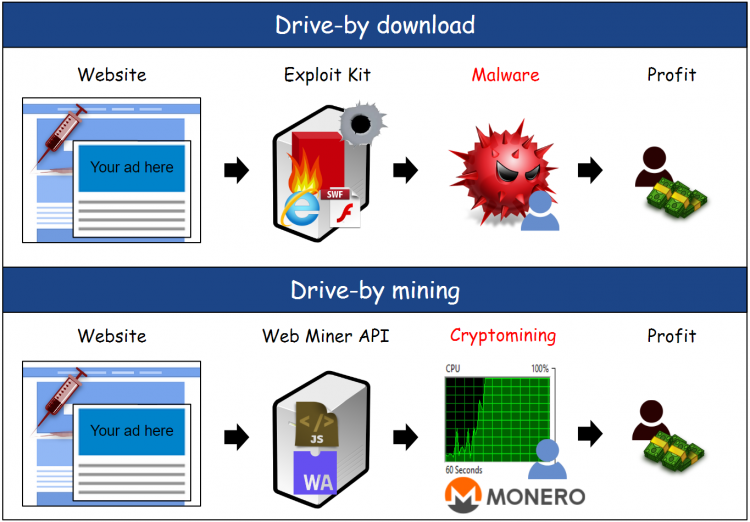
In his latest review, Jérôme writes about a slight reversal of an important shift seen in the past year: that of a shift from exploit kits delivering malware to the endpoint, to malicious or compromised websites mining for cryptocurrencies inside the browser.
It is this shift that was the focus of the paper he presented at VB2018 in Montreal earlier this month. In this well-researched paper, he describes how and why exploit kits shifted from delivering malware to in-browser mining. Even if the reversal were to continue, the paper really helps understand the threat of web-based attacks and the cybercriminal business model behind it.
We have now published Jérôme's paper in both HTML and PDF format. We have also uploaded the video of his presentation to our YouTube channel.