Posted by Martijn Grooten on Nov 27, 2018
Extremely targeted attacks aside, when a user gets infected through the web, it means something has happened that should not have. Either the user clicked on a link they shouldn't have clicked on, or they were browsing the web using unpatched software.
Unfortunately, in both large and small organisations, these things happen a lot. And this is why most organisations use a web security solution as an additional layer of security.
 In our regular VBWeb tests, Virus Bulletin measures the performance of web security gateways to ensure they deliver their promise of seriously mitigating the risks. In the latest VBWeb test report, published last week, products from Kaspersky Lab, Trustwave and Fortinet all achieved VBWeb certification by blocking a high percentage of active threats while avoiding false positives.
In our regular VBWeb tests, Virus Bulletin measures the performance of web security gateways to ensure they deliver their promise of seriously mitigating the risks. In the latest VBWeb test report, published last week, products from Kaspersky Lab, Trustwave and Fortinet all achieved VBWeb certification by blocking a high percentage of active threats while avoiding false positives.
The fact that the latter two products missed some early instances of the then new Fallout exploit kit (discovered in September by security researcher nao_sec) emphasises that this isn't a trivial task: exploit kits have declined in prevalence in recent years, but are doing a very good job of staying hidden from security researchers.
Later instances of Fallout – which continues to be active – were detected by all products, and all of them also blocked all instances of in-browser cryptocurrency miners and almost all direct malware downloads.
Virus Bulletin offers a wide range of private and public testing opportunities. For more information on what we can do for your product, contact us at [email protected].
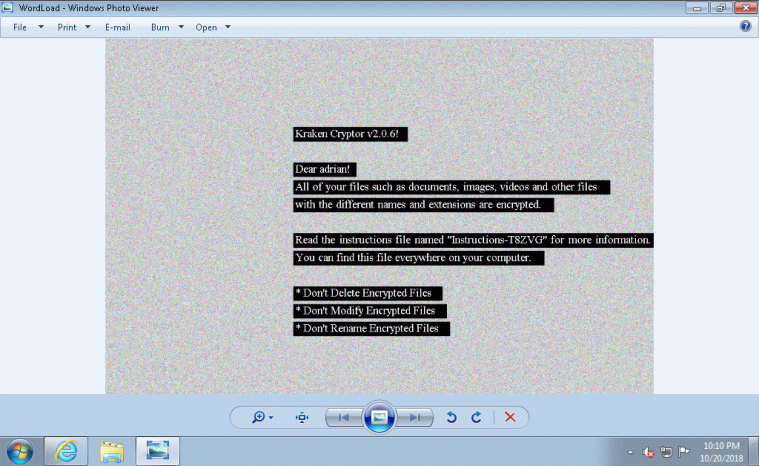 The Kraken Cryptor ransomware was one of the instances of malware seen during the test.
The Kraken Cryptor ransomware was one of the instances of malware seen during the test.