Posted by Martijn Grooten on Oct 24, 2019
The web continues to be a major infection vector for individuals and organisations alike. Though the number of drive-by download attacks (often through exploit kits) is down from its peak half a decade ago, they have seen a bit of resurgence recently, with more than half a dozen exploit kits currently active ─ and tracked in the Virus Bulletin lab.
At the same time, links in emails are often use to spread malware, thus combining these two most common infection vectors. In our email security tests we have repeatedly shown that emails with a malicious link are less likely to be blocked than those with a malicious attachment, and indeed many active malware campaigns spread this way.
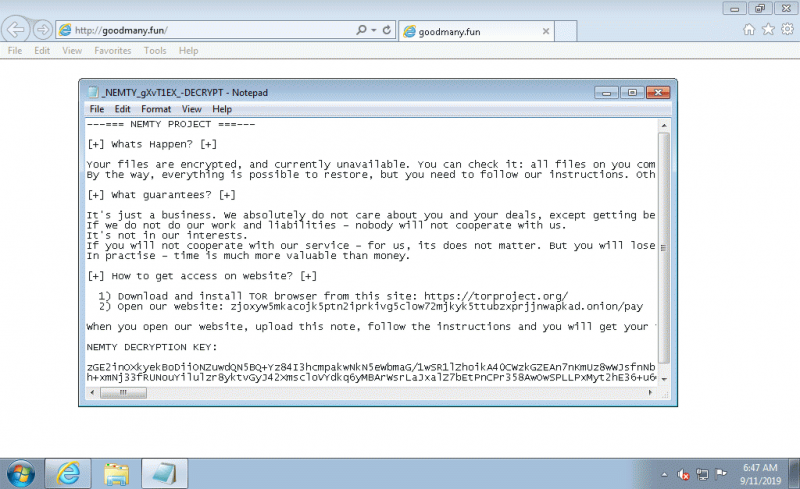 The Nemty ransomware as downloaded by the Radio exploit kit.
The Nemty ransomware as downloaded by the Radio exploit kit.
And not all bad URLs contain malware: the market for stolen credentials continues to make phishing for credentials an easy way for criminals to make money – indeed, we see a great many phishing URLs active every day.
Though good security against web-based threats involves a multi-layered approach that includes endpoint security, regular patching and multi-factor authentication, web security products can prevent the user from accessing malicious URLs in the first place.
In our VBWeb tests, we have been testing many web security products for their ability to block such threats. Like all of VB's tests, we can test products either privately or publicly, and like all VB tests the test combines certification with performance measurement in various categories. The quarterly reports (most recently Autumn 2019) also provide a good overview of the web threat landscape.
In our test lab, we can test both cloud-based and on-premise solutions, and also look at the performance of URL- or domain-based blocklists. We are currently working on the integration of endpoint-based security products.
If you are interested in having your product tested, or discussing the options with us, do contact us at [email protected].
