2005-09-01
Abstract
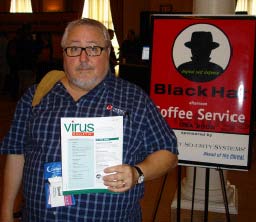
Although one always hears about 'Black Hat and DEFCON', they are in fact two very different events. VB's intrepid reporter (aka AV industry miscreant) has a report on each.
Copyright © 2005 Virus Bulletin
 A wise man once told me that the difference between responsibility and blame is that responsibility happens before the fact, and blame happens after the fact. Bear that in mind.
A wise man once told me that the difference between responsibility and blame is that responsibility happens before the fact, and blame happens after the fact. Bear that in mind.
I went to Las Vegas in July to attend both the Black Hat Briefings and DEFCON, at the behest of Virus Bulletin, who had asked me to write up a report of the proceedings as I saw them. So without digressing, I will get right to the subject at hand.
Now, you always hear about 'Black Hat and DEFCON', so just to set the record straight, the two are very different things. Black Hat is a very serious conference intended to illustrate top issues in the world of network security, and DEFCON is a 'through-the-rabbit-hole' con, where not only is everyone there a poseur, but everyone is proud to admit that everyone there is a poseur.
When registering for Black Hat, you are given a backpack containing the conference proceedings (a paperback volume the size of a very large phonebook) and a number of other useful items. A closer inspection of the proceedings volume showed that the rumours were true - a whole presentation had been torn neatly out of the volume - and the CD versions of the proceedings had been rudely withdrawn to a secret location where each was ceremonially destroyed under the watchful eye of a trained exorcist.
The missing presentation was Michael Linn's CISCO disclosure - a subject so controversial that no two people agree on what it really means. You cannot see the slides, you cannot see the video or hear the audio recordings made of the presentation (both were seized by a local court following a cease and desist order), and you can't get a clear story about exactly what happened, but I will tell you this about Michael's presentation: it was really crowded! After standing and listening to about 15 minutes (including the famous 'Welcome to the Eighties' line - upon which I will not elaborate here) I did what any other reasonable conference-goer would do - I went to another room, to let everyone else report on the big enchilada.
I ended up in a panel on certification, listening to a very august panel discuss, among other things, common criteria and other government mandated certs. A notable miscreant from the AV industry made comment that NIAP certification (US common criteria testing and certification) was overpriced and functionally useless - typically taking much longer than the product's shelf life to achieve. This led to a long series of hallway discussions with both government and private industry types.

A notable miscreant from the AV industry (aka David Perry).
After lunch was a presentation entitled 'Owning anti-virus: weaknesses in a critical security component', by Alex Wheeler and Neel Mehta. These very earnest guys had some great tips for breaking applications, like 'take lots of notes in notepad' and 'print everything out and write in the margins'. They detailed three vulnerabilities, one each in Trend Micro, Symantec and McAfee anti-virus programs. Apparently none of these items will work on a current version. To their great credit, Wheeler and Mehta were very generous with their praise for the anti-virus industry, noting that AV products were 'much safer than anything else in the industry' and that 'patches and fixes are regularly updated'. (Patches and fixes? Isn't that pretty much all we do?)
Of course, another miscreant from the AV industry stood up in the question and comment section and asked why they did not discuss the vulnerability that led to the WITTY worm. Since both speakers were employed at ISS, this was largely a rhetorical question.

Another miscreant from the AV industry (aka Andrew Lee).
The rest of the day was taken up with a lot of very amazing discoveries (long range RFID detection, more pod cast interviews, and a very interesting reception).
Day two of the Black Hat Briefings contained the same four tracks as day one: Applications Security, Forensics, Privacy and Zero Day Defense. There were way too many presentations for any one person to see, so it is a good thing that all of the presentation slides are given to every attendee in a large book (it builds character to carry this albatross for two days, not to mention muscles). There was a new product announcement from Phil Zimmerman (secure VoIP) and a corresponding hack discussion about something called 'SIP fuzzing' (you could never make this stuff up) which is ostensibly either a way to break VOIP security, or a tasty beverage.
My final session at Black Hat was on the US national ID card. Now, as a US citizen, I have a passport, a driver's licence, a Social Security number, a medical insurance card, several credit cards, a COSTCO membership ID, an auto club card, a library card, a dental plan card, an ID card for my office, an ATM card and an annual passport to Disneyland. My wallet is at least an inch thick, and is already causing spinal displacement in an adult American male. So now there is some need for a national ID card?
Apparently this is an issue of great significance and controversial impact. Each of the panel members had something unrelated and, well, totally ambiguous to say about the national ID card program. Like any great panel discussion, this muddied the waters beyond all possibility of repair. And each panellist took great pains to discuss the national ID card issue in light of the WTC bombings of 9/11/01. (I know this is an English publication, but we Americans insist on listing dates out of order.)
Good thing a noted miscreant from the AV industry (noticing a pattern here?) stood up and asked a question that brought thunderous applause from the crowd.
Black Hat is a full week long between the seminars and briefings, and is a very high content security seminar. If you are a professional in this industry you would be well served to attend the Black Hat Briefings at the very least. It is quite expensive, but very informative. One industry professional (who shall remain nameless) is quoted saying, 'At Black Hat you hear first about what you spend the next year fighting'. Sure, his syntax is tested to its theoretical limits, but the lesson is clear: this conference is the real thing. To be responsible, find out ahead of time.
DEFCON is an old Paiute Indian word meaning 'many black T-shirts for sale' and is billed as 'the largest hacker gathering on planet earth'. DEFCON (which is actually named for the old pre-colour-code national defence alert status) is everything that Black Hat is not. DEFCON is immensely silly, yet frequently takes itself too seriously. DEFCON is only the weekend long, incorporates games like 'Spot the Fed', 'Capture the Flag', and competitions like 'WarDriving' and 'Lock Picking'. Where BH is aimed at the system administrator learning to protect his network, DC is aimed at the '1337' kid trying to break into something. There is a lot of hair dye at DEFCON.
DEFCON has the most amazing check-in of any computer conference or show in the whole world. Those familiar with conferences know that registering or checking in often means filling out a long form where people try to find out how to sell your soul to a marketing organization.
At DEFCON, you stand in a line at the Alexis Park hotel to pay 80 dollars in cash, in exchange for which you are handed a badge, a CD and a conference schedule the size of a pamphlet, then hustled out the door by a person officially designated as 'goon'. Not only do they not care whether you buy networking equipment for your company, they don't even want to know your name! For 80 dollars (cash) at a hacker convention, everyone is who they say they are (or nobody is).
The conference badge itself is a wonder to behold. This year's was a rectangle of day-glo Perspex with die cut punches to spell out DEFCON 13, the bearer's designation (HUMAN, in my case) and the charming happy face skull and crossbones logo of DEFCON. Each year's badge is a different and unique design.
The Alexis Park has no casino, and the lobby is the main hangout for attendees. There were a pair of ATM machines in the lobby, each proudly displaying a DEFCON 13 logo on the screen. Very few people actually used the ATM ... it is suspect of being owned, or worse.
During the entire weekend, hackers sit in a ballroom trying to capture the flag. Any system broken is displayed (with the user's photo) on the 'WALL OF SHEEP'. These young men (and a small but growing number of women) are too focused to speak, eat or sleep - they are there simply to hack.
Presentations covered a large number of topics, none quite as memorable as 2004's presentation by a drunken self-professed virus writer in a kilt, but I shan't detail the DEFCON presentations (see http://www.defcon.org/ for a complete listing).
DEFCON also featured a dealer's room, where one can find antennae (for WarDriving), t-shirts books, stickers, lock picks, and surplus electronic gear.
DEFCON might consist mainly of poseurs, as many say, but it is the mythic heart of the hacker world. I don't imagine I will miss it ever again. It's worth at least a look.
If you fly over Las Vegas at night you can see the brightest lit mile of any street in the world. Dazzling neon and flashing lights display each casino in what looks, from the air, like a toy, or a brilliant trap set on the pitch black desert night, a trap to catch the superstitious, the illogical, the cocky. Las Vegas hates computer geeks - you know, we don't tend to gamble much per person. There is one good reason for that: we can do the math.