Posted by Virus Bulletin on Oct 13, 2014
Jean-Ian Boutin looks at the increased commoditization of webinjects.
Virus Bulletin has always been about sharing information, and the Virus Bulletin conference is an important part of that. We would love to be able to share some of the discussions attendees had during the lunch and coffee breaks, the late-night or early-morning meetings in the hotel lobby, and the inspiration one gets from being around such bright minds.
Of course, we are unable to do that. But what we can do is share some of the technical content presented during VB2014. Over the next months, we will be sharing conference papers as well as video recordings of the presentations. We start off this series with the paper "The evolution of webinjects" by ESET researcher Jean-Ian Boutin.
Webinjects, where the trojan modifies the content of a targeted website on the fly before displaying it in the browser, have become ubiquitous in today's banking trojans. They are used for a wide range of malicious activities to aid financial fraud, from phishing for credentials to bypassing two-factor authentication.
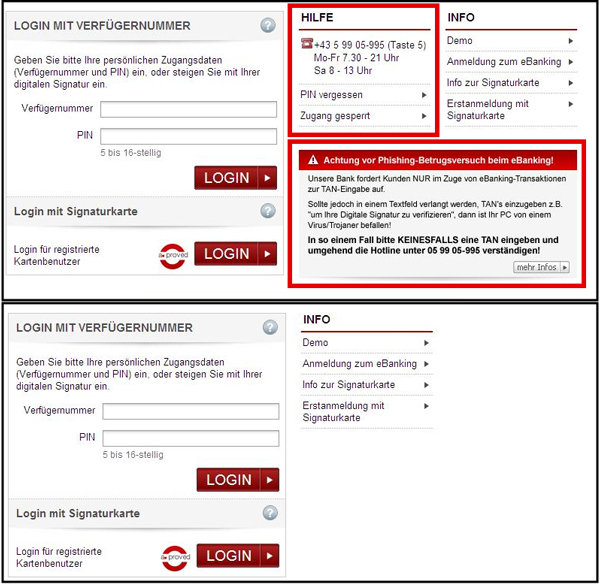
In his paper, Jean-Ian looks at how webinjects have evolved over time. Banks are constantly improving the security of their online systems, and the use of webinjects is one way in which malware authors are trying to keep up. In many of today's banking trojans, webinjects are the core of the attack code.
In line with a general trend in cybercrime, webinjects have become increasingly commoditized. As a consequence, most modern banking trojans are now using the same format for the webinject configuration file.
Malicious actors, many of whom have ties with traditional organized crime groups, sell such configuration files on underground forums, allowing crooks operating banking malware to target many financial institutions without having to reverse engineer the format used for online transactions by each individual institution.

You can read Jean-Ian's paper here in HTML-format, or download it here as a PDF (no registration or subscription required). You can download the presentation slides here. We have also uploaded the presentation to our YouTube channel.