Posted by Virus Bulletin on Nov 21, 2014
Many VB authors and presenters to speak at second botnet-fighting conference.
Last year, I attended the first edition of 'Botconf' in the French city of Nantes. I really enjoyed the conference, so I am looking forward to the second edition, which will take place in less than two weeks' time in Nancy, in Northeastern France.
I was also pleased to see that several of this year's Botconf speakers have either spoken at recent VB conferences or published articles through Virus Bulletin.

G Data researcher Paul Rascagnères will present a workshop on using WinDBG to analyse rootkits and is co-author of a paper on the 'Havex' RAT that will also be presented at the conference. Earlier this year, we published a paper by Paul on the 'IcoScript' RAT.
At VB2014, CloudFlare's Nick Sullivan presented a paper on DNSSEC and also participated in the closing panel. At Botconf, he will speak about this year's botnet attack trends.
OpenDNS researcher Dhia Mahjoub took to the VB2014 stage twice: first to speak about using the ASN graph to detect malicious networks (a paper we published today), and then with his colleague Thibault Reuille, to speak about security analytics with a 3D visualization engine. At Botconf, Dhia (together with Hendrik Adrian, of MalwareMustDie) will speak about taking a new look at fast-flux networks.
Those with an interest in mobile malware will hopefully have read the paper we published earlier this year, in which Fortinet researchers Axelle Apvrille and Ruchna Nigam took a look at obfuscation in Android malware. Ruchna will speak at Botconf about a timeline of mobile botnets.
Another platform that has seen an increased interest from those running botnets is *nix - in particular *nix web servers. Yandex researchers Evgeny Sidorov and Andrew Kovalev will speak on this topic in Nancy. The same group of researchers published a paper on the 'Mayhem' malware earlier this year, while at VB2014, Evgeny spoke about 'Ebury' and 'Cdorked', together with ESET's Pierre-Marc Bureau.
In their presentation on multiplatform DDoS botnets, Avast researchers Peter Kalnai and Jaromir Horejsi will also focus primarily on Linux and OpenBSD. At VB2014, they presented a paper on click fraud.
A few years ago, Trend Micro's David Sancho spoke at a number VB conferences and seminars. At Botconf, he will speak on 'Operation Emmental', in which banking malware defeats two-factor authentication.
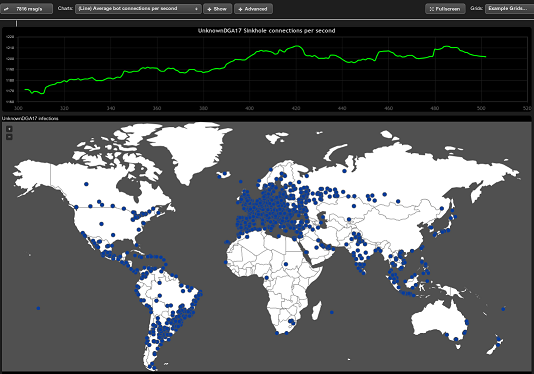
Finally, I will speak at the event as well. Together with Joao Gouveia of AnubisNetworks, we will speak about the 'Mevade' (or 'Sefnit') botnet - research that was published by AnubisNetworks here.
Botconf takes place 3-5 December in Nancy, France. Registration is still possible, but closes 26 November at noon CET.
Posted on 21 November 2014 by Martijn Grooten