Posted by Virus Bulletin on Mar 19, 2015
Patrick Wardle shows how OS X is also vulnerable to once common Windows attacks.
A few years ago, DLL hijacking on Windows was really hot, despite the fact that the concept had been discussed by none other than the NSA as far back as 1998.
Many applications load dynamic link libraries (DLLs) without specifying a path name to indicate where the library is to be found in the operating system. When such a path name is absent, the operating system looks for the DLL file in a number of well-defined directories. An attacker could thus 'hijack' the DLL by placing a rogue DLL file into one of those directories, so that the operating system will find the rogue DLL first.
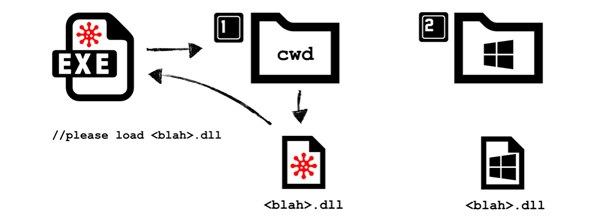
Patching vulnerabilities and the introduction of a number of OS-level mitigations has made DLL hijacking much less of an issue on Windows these days. But could other operating systems, such as Mac OS X, be vulnerable to a similar kind of attack?
This is what Synack researcher Patrick Wardle wondered. He set himself the task of finding a way to make OS X applications load arbitrary binaries.
Today, he presents the results of his research at the CanSecWest conference in Vancouver. He has also written a paper providing the technical details of his research - which Virus Bulletin has also published today.
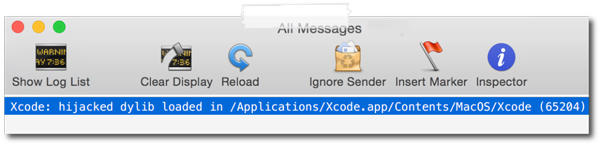
It turns out that OS X is vulnerable to this kind of attack - which is known as 'Dylib hijacking' in this case. In his paper, Patrick takes the reader through his search for flaws, making it an excellent read for anyone who wants to harden the operating system by looking for these kinds of logic flaws.
Dylib hijacking is not as trivial as DLL hijacking once was on Windows and, of course, being able to make a vulnerable application load a rogue binary still requires the attacker to store the library on the target's machine. As such, the attack is more suitable for making an existing infection maintain persistence (a subject that Patrick spoke about at VB2014) than as an infection vector.
Moreover, Patrick shows how a man-in-the-middle attacker could use only a very small amount of social engineering to bypass Apple's Gatekeeper, which is supposed to prevent malicious content from being loaded on OS X.
You can read the paper here in HTML format or here as a PDF. (Remember that all content published by Virus Bulletin can be read free of charge, with no registration required.)
Posted on 19 March 2015 by Martijn Grooten