Posted by Martijn Grooten on Aug 9, 2018
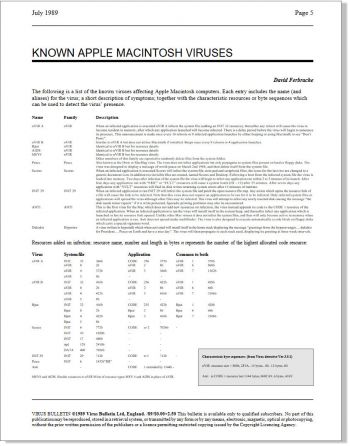
The very first edition of Virus Bulletin magazine, published in July 1989, contained lists of "[all] known IBM PC viruses" and "[all] known Apple Macintosh viruses". In the pre-web days, people really did have to rely on a printed magazine to update them on the latest threats, and thus Virus Bulletin was one of the first providers of threat intelligence.
Throughout its history, Virus Bulletin has been actively involved in threat intelligence, not only as a provider but even more so as a facilitator. After all, the VB Conference has long been one of the prime places where security experts gather to exchange data and to build those connections that are essential for intelligence sharing.
Thus we are very excited to announce a special summit, part of VB2018, that is dedicated to threat intelligence. The "Threat Intelligence Summit" ("TIS") will take place on Friday 5 October – we will announce the programme for the Summit soon, but can already let you know that it will feature a good mix of experts dealing with various aspects of threat intelligence.
The TIS will be incorporated as part of the three-day VB conference, though as places for the Summit will be limited, we will ask those wishing to attend to register their intent during the VB Conference ticket-buying process. Note (30 August 2018) that no special registration will be required after all.
Of course, many talks on the main VB2018 programme deal either explicitly or implicitly with threat intelligence, and whether you're a provider or a consumer of threat intelligence data, the full VB2018 event is worth attending.