Posted by Martijn Grooten on Oct 23, 2019
Targeted ransomware has become one of the biggest and most damaging cybercrime trends in recent years. 'Targeted' is a bit of a misnomer though: the operators of the ransomware rarely choose the victim organisations. Instead, they have the organisations 'chosen' through an infection with another piece of malware that is then used as a foothold for the ransomware.
Quite often, this malware is Emotet, which made a spectacular comeback in September. The ransomware is deployed often through a second malware family like Trickbot. Various ransomware families are making use of this scheme to be installed on high-value networks, with Ryuk being one of the most prominent.
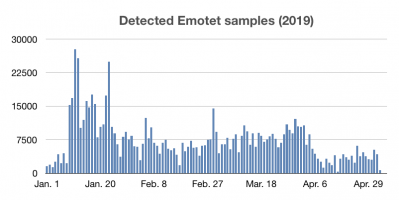 Detected Emotet samples on a daily basis in 2019.
Detected Emotet samples on a daily basis in 2019.
A good understanding of Emotet and an ability to defend against it will allow one to fend off many sophisticated targeted attackers, while an understanding of Ryuk and similar ransomware families will aid an overall understanding of how such malware then spreads through an internal network.
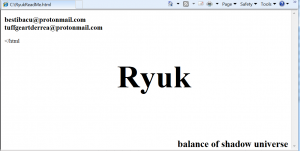 Ryuk ransom note.
Ryuk ransom note.
Today we publish two relevant papers presented at VB2019, the 29th Virus Bulletin Conference. Sophos researcher Luca Nagy presented a paper on Emotet, while Deloitte researchers Gabriela Nicolao and Luciano Martins presented one on Ryuk. In addition to the respective papers, we have also uploaded the videos of the presentations to our YouTube channel.
