Posted by Martijn Grooten on Nov 5, 2019
The sharp rise in Android malware in recent years has led security researchers to look for efficient ways to cluster related samples, especially since the tools used for Windows malware don't always work well for other platforms.
Today, we publish a paper by Shinho Lee, Wookhyun Jung, Sangwon Kim, Jihyun Lee, Jun-Seob Kim, all researchers from ESTsecurity in South Korea. In it, they propose 'Dexofuzzy', a fuzzy hash based on opcode inside Dex files. As such, the hash is tailored for Android samples.
In their paper, they demonstrate how Dexofuzzy could be used to find 74 clusters in a large dataset of Android malware.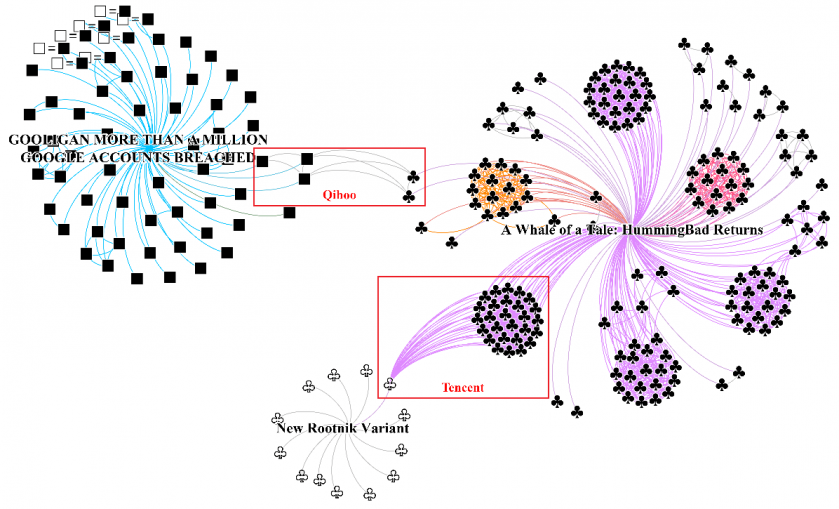 Clustering malware samples by types of packers.
Clustering malware samples by types of packers.
You can read the paper in both HTML and PDF format. Those interested in fuzzy hashes and their application to clustering of large malware datasets may also want to read a paper published in 2015 in which Brian Wallace looks at ssDeep, the algorithm which forms the basis of Dexofuzzy.
