Below are some details of the VB2022 posters.
 |
AndroscopeAxelle Apvrille, Fortinet Need to find an Android malware using a native library? intercept SMS? You’ve analysed one recently... but what’s its hash? Arg! Can’t find it! Where is it?! Tired of searching? Androscope is your friend! |
 |
The State of OSINTJason Zhang, Anomali Open source threat intelligence (OSINT) has grown significantly in recent years and become increasingly important in better understanding the cyber threat landscape. Security professionals often use OSINT to help identify network weaknesses and strengthen security solutions. There also exist big challenges with OSINT, such as information overload, uncertainty management and data quality. In this poster, we provide our study to reflect the current state of OSINT and aim to help alleviate the challenges in dealing with OSINT. More specifically, we focus our analysis on the following aspects: intelligence sources, intelligence collected by Anomali, top 10 malware attribution, and analysis of false positives. |
 |
UEFI trojanOleg Bil, State Technical Service |
 |
Latest methods in real-time threat intelligenceArnie Bjorklund, SURBL How are URL shorteners used to bypass email security solutions and what can we do about them? |
 |
A new business model for the InternetKenneth Bechtel, Massive Computing Software monetization is currently dominated by adware, as we are aware this is inherently insecure and provides multiple inequities of payment to the vendors, inconveniences to end users, and lack of control of what content is delivered. A newer model, that leverages the vision of SETI online, creating a Distributing Computing Opt-In model exits and is more secure and less intrusive. We will discuss this model and how it can be leveraged in a secure, reliable manner for multiple uses including but not limited to universities, medical facilities and even in an environmentally and trustworthy manner of legal coin mining. |
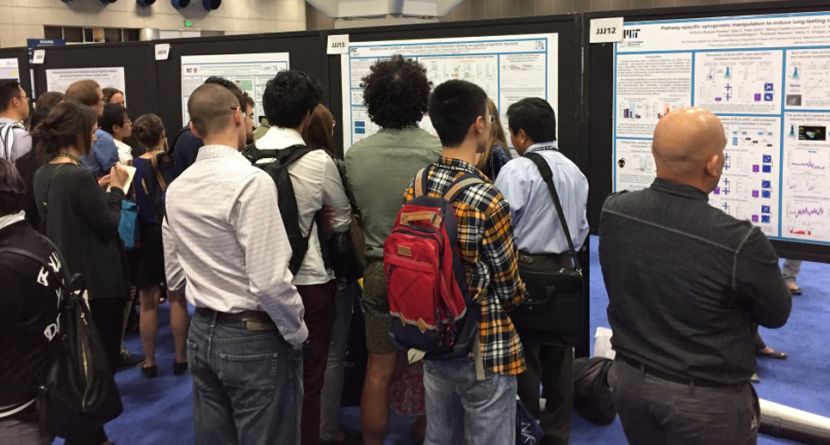
A poster session is a room in which multiple presenters stand next to posters that outline their topic in brief. Delegates wander around the room reading the posters and stopping to talk to the presenters when they have questions or want more information - each presenter being ready to elaborate on their poster with a brief (less than 5 minutes) explanation.
For presenters, a poster presentation is a great way to communicate your research in a very concise format and build connections.
For delegates, poster sessions are a great way to find out about new projects, topics, research, and meet with researchers in a quick and efficient way – making new contacts along the way.
 Source: Scientifica
Source: Scientifica